| Home | Sources Directory | News Releases | Calendar | Articles | | Contact | |
Espionage
Espionage or spying involves an individual obtaining information that is considered secret or confidential without the permission of the holder of the information. Espionage is inherently clandestine, lest the legitimate holder of the information change plans or take other countermeasures once it is known that the information is in unauthorized hands.
Espionage is usually part of an institutional effort by a government or corporation, and the term is most readily associated with state spying on potential or actual enemies, primarily for military purposes. Spying involving corporations is known as industrial espionage. Government surveillance of civil society groups, social movements, and individuals involved in political activism, such as COINTELPRO conducted by the FBI, is not covered by the present article.
See clandestine HUMINT for the basic concepts of such information collection, and subordinate articles such as clandestine HUMINT operational techniques and clandestine HUMINT asset recruiting for discussions of the tradecraft used to collect this information.
[edit] History
Incidents of espionage are well documented throughout history. The ancient writings of Chinese and Indian military strategists such as Sun-Tzu and Chanakya contain information on deception and subversion. Chanakya's student Chandragupta Maurya, founder of the Maurya Empire in India, made use of assassinations, spies and secret agents, which are described in Chanakya's Arthasastra. The ancient Egyptians had a thoroughly developed system for the acquisition of intelligence, and the Hebrews used spies as well, as in the story of Rahab. Spies were also prevalent in the Greek and Roman empires.[1] During the 13th and 14th centuries, the Mongols relied heavily on espionage in their conquests in Asia and Europe. Feudal Japan often used ninja to gather intelligence. More recently, spies played a significant part in Elizabethan England (see Francis Walsingham). Many modern espionage methods were well established even then.[2]
The Cold War involved intense espionage activity between the United States of America and its allies and the Soviet Union and the People's Republic of China and their allies, particularly related to nuclear weapons secrets. Recently, espionage agencies have targeted the illegal drug trade and those considered to be terrorists.
Different intelligence services value certain intelligence collection techniques over others. The former Soviet Union, for example, preferred human sources over research in open sources, while the United States has tended to emphasize technological methods such as SIGINT and IMINT. Both Soviet political (KGB) and military intelligence (GRU[3]) officers were judged by the number of agents they recruited.
[edit] Targets of espionage
Espionage agents are usually trained experts in a specific targeted field. This allows them to differentiate mundane information from a target which has intrinsic value to own organisational development. Correct identification of the target at its execution is the sole purpose of the espionage operation.
The broad areas of espionage targeting expertise are:
- Natural resource strategic production identification and assessment (food, energy, materials)
- Agents are usually found among bureaucrats that administer these resources in own countries
- Popular sentiment towards domestic and foreign policies (popular, middle class, elites)
- Agents often recruited from field journalistic crews, exchange postgraduate students and sociology researchers
- Strategic economic strengths (production, research, manufacture, infrastructure)
- Agents recruited from science and technology academia, commercial enterprises, and more rarely from military technologists
- Military capability intelligence (offensive, defensive, manoeuvre, naval, air, space)
- Agents are trained by special military espionage education facilities, and posted to area of operation with covert identities to prevent prosecution
[edit] Methods and terminology
While news media may speak of "spy satellites" and the like, espionage is not a synonym for all intelligence functions. It is a specific form of human source intelligence (HUMINT). Codebreaking (cryptanalysis or COMINT), aircraft or satellite photography (IMINT) and research in open publications (OSINT) are all intelligence gathering disciplines, but none of them are espionage. Many HUMINT activities, such as prisoner interrogation, reports from military reconnaissance patrols and from diplomats, etc., are not espionage.
Unlike other forms of intelligence collection disciplines, espionage usually involves accessing the place where the desired information is stored, or accessing the people who know the information and will divulge it through some kind of subterfuge. There are exceptions to physical meetings, such as the Oslo Report, or the insistence of Robert Hanssen in never meeting the people to whom he was selling information.
The US defines espionage towards itself as "The act of obtaining, delivering, transmitting, communicating, or receiving information about the national defense with an intent, or reason to believe, that the information may be used to the injury of the United States or to the advantage of any foreign nation. Black's Law Dictionary (1990) defines espionage as: "...gathering, transmitting, or losing...information related to the national defense". Espionage is a violation of United States law, 18 U.S.C. – 792'798 and Article 106 of the Uniform Code of Military Justice".[4] The United States, like most nations, conducts espionage against other nations, under the control of the National Clandestine Service. Britain's espionage activities are controlled by the Secret Intelligence Service.
[edit] Organization
A spy is a person employed to obtain such secrets. Within the United States Intelligence Community, "asset" is a more common usage. A case officer, who may have diplomatic status (i.e., official cover or non-official cover) supports and directs the human collector. Cutouts are couriers who do not know the agent or case officer, but transfer messages. A safe house is a refuge for spies.
In larger networks the organization can be complex with many methods to avoid detection, including clandestine cell systems. Often the players have never met. Case officers are stationed in foreign countries to recruit and to supervise intelligence agents, who in turn spy on targets in their countries where they are assigned. A spy need not be a citizen of the target country. While the more common practice is to recruit a person already trusted with access to sensitive information, sometimes a person with a well-prepared synthetic identity, called a legend in tradecraft, may attempt to infiltrate a target organization.
These agents can be moles (who are recruited before they get access to secrets), defectors (who are recruited after they get access to secrets and leave their country) or defectors in place (who get access but do not leave).
Spies may also be used to spread disinformation in the organization in which they are planted, such as giving false reports about their country's military movements, or about a competing company's ability to bring a product to market. Spies may be given other roles that also require infiltration, such as sabotage.
Many governments routinely spy on their allies as well as their enemies, although they typically maintain a policy of not commenting on this. Governments also employ private companies to collect information on their behalf such as SCG International Risk and others.
[edit] Industrial espionage
Canada is losing $12 billion a year due to industrial espionage.[5] It is estimated that German companies were losing about '50 billion ($87 billion) and 30,000 jobs to industrial espionage every year.[6]
[edit] Agents in Espionage
"An Agent is someone that has been authorized to function on behalf of another."[7] A "covert human intelligence source."[8]
- Double agent, "is a person who engages in clandestine activity for two intelligence or security services (or more in joint operations), who provides information about one or about each to the other, and who wittingly withholds significant information from one on the instructions of the other or is unwittingly manipulated by one so that significant facts are withheld from the adversary. Peddlers, fabricators, and others who work for themselves rather than a service are not double agents because they are not agents. The fact that doubles have an agent relationship with both sides distinguishes them from penetrations, who normally are placed with the target service in a staff or officer capacity."[9]
- Re-doubled agent, an agent who gets caught as a double agent and is forced to mislead the foreign intelligence service.
- Unwitting double agent, an agent who offers or is forced to recruit as a double or re-doubled agent and in the process is recruited by either a third party intelligence service or his own government without the knowledge of the intended target intelligence service or the agent. This can be useful in capturing important information from an agent that is attempting to seek allegiance with another country. The double agent usually has knowledge of both intelligence services and can identify operational techniques of both, thus making third party recruitment difficult or impossible. The knowledge of operational techniques can also effect the relationship between the Operations Officer (or case officer) and the agent if the case is transferred by an Operational Targeting Officer to a new Operations Officer, leaving the new officer vulnerable to attack. This type of transfer may occur when an officer has completed his term of service or when his cover is blown.
- Triple agent, an agent that is working for three intelligence services.
- Unwitting double agent, an agent who offers or is forced to recruit as a double or re-doubled agent and in the process is recruited by either a third party intelligence service or his own government without the knowledge of the intended target intelligence service or the agent. This can be useful in capturing important information from an agent that is attempting to seek allegiance with another country. The double agent usually has knowledge of both intelligence services and can identify operational techniques of both, thus making third party recruitment difficult or impossible. The knowledge of operational techniques can also effect the relationship between the Operations Officer (or case officer) and the agent if the case is transferred by an Operational Targeting Officer to a new Operations Officer, leaving the new officer vulnerable to attack. This type of transfer may occur when an officer has completed his term of service or when his cover is blown.
- Re-doubled agent, an agent who gets caught as a double agent and is forced to mislead the foreign intelligence service.
There are several types of agent in use today.[10]
- Double agent, These agents always require special handling as they can become re-doubled if caught. Special handling may include debriefing with an Operations Officer whose cover has already been blown and verifying intelligence reports immediately in order to establish trust.
- Intelligence agent: Provides access to sensitive information through the use of special privileges. If used in corporate intelligence gathering, this may include gathering information of a corporate business venture, stock portfolio, or the creation of a new menu item at a restaurant. In economic intelligence, "Economic Analysts may use their specialized skills to analyze and interpret economic trends and developments, assess and track foreign financial activities, and develop new econometric and modeling methodologies."[11] This may also include information of trade or tariff.
- Access agent: Provides access to other potential agents by providing profiling information that can help lead to recruitment into an intelligence service.
- Agent of influence: Someone who may provide political influence in an area of interest or may even provide publications needed to further an intelligence service agenda. I.e. The use of the media to print a story to mislead a foreign service into action, exposing their operations while under surveillance.
- Agent provocateur: This type of agent will instigate trouble or may provide information to gather as many people as possible into one location for an arrest.
- Facilities agent: A facilities agent may provide access to buildings such as garages or offices used for staging operations, resupply, etc.
- Principle agent: This agent functions as a handler for an established network of agents usually Blue Chip.
- Confusion agent: May provide misleading information to an enemy intelligence service or attempt to discredit the operations of the target in an operation.
- Sleeper agent: A sleeper agent is a person who is recruited to an intelligence service to wake up and perform a specific set of tasks or functions while living under cover in an area of interest. This type of agent is not the same as a deep cover operative who is continually in contact with their case officer in order to file intelligence reports. A sleeper agent will not be in contact with anyone until activated.
- Illegal agent: This is a person who is living in another country under false credentials that does not report to a local station. A non official cover operative is a type of cover used by an intelligence operative and can be dubbed an "Illegal"[12] when working in another country without diplomatic protection.
[edit] Risks
The risks of espionage vary. A spy breaking the host country's laws may be deported, imprisoned, or even executed. A spy breaking his/her own country's laws can be imprisoned for espionage or/and treason, or even executed, as the Rosenbergs were. For example, when Aldrich Ames handed a stack of dossiers of CIA agents in the Eastern Bloc to his KGB-officer "handler", the KGB "rolled up" several networks, and at least ten people were secretly shot. When Ames was arrested by the FBI, he faced life in prison; his contact, who had diplomatic immunity, was declared persona non grata and taken to the airport. Ames's wife was threatened with life imprisonment if her husband did not cooperate; he did, and she was given a five-year sentence. Hugh Francis Redmond, a CIA officer in China, spent nineteen years in a Chinese prison for espionage'and died there'as he was operating without diplomatic cover and immunity.
Many organizations, both national and non-national, conduct espionage operations. It should not be assumed that espionage is always directed at the most secret operations of a target country. National and terrorist organizations and other groups are also targets.
Communications both are necessary to espionage and clandestine operations, and also a great vulnerability when the adversary has sophisticated SIGINT detection and interception capability. Agents must also transfer money securely.
See espionage organizations for national and non-national groups that conduct clandestine human operations, for reasons that may include: assessment of national capabilities at the strategic level, warning of the movements of security and military organizations; financial systems; protective measures around targets.
[edit] Spies in various conflicts
|
|
This article is in a list format that may be better presented using prose. You can help by converting this article to prose, if appropriate. Editing help is available. (March 2010) |

[edit] Espionage under Elizabeth I of England
[edit] Espionage in the American Revolution
[edit] Espionage in the Napoleonic Wars
[edit] Espionage in the American Civil War
One of the innovations in the American Civil War was the use of proprietary companies for intelligence collection. See Allan Pinkerton.
[edit] Espionage in the Aceh War
Dutch professor Snouck Hurgronje world leading authority on Islam was a proponent of espionage to quell muslim resistance in Aceh in the Dutch East Indies. In his role as Colonial Advisor of Oriental affairs he gathered inteligence under the name "Haji Abdul Ghaffar".
His knowledge of Islamic and Aceh culture enabled him to devise strategies which significantly helped crush the resistance of the Aceh inhabitants and impose Dutch colonial rule on them, ending the 40 year Aceh War with varying casualty estimates of between 50,000 and 100,000 inhabitants dead and about a million wounded.
[edit] Espionage in the Second Boer War
[edit] Espionage in World War I
[edit] Espionage in World War II
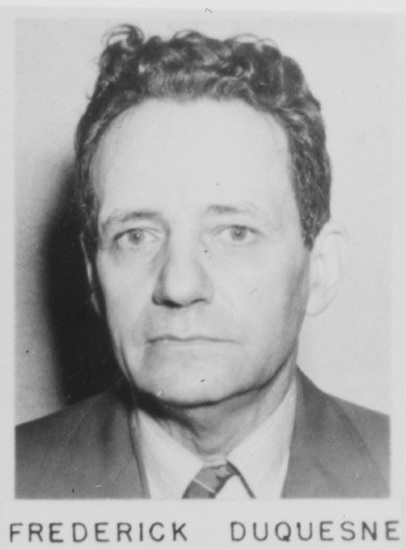
Informants were common in World War II, examples include the Oslo Report that warned the British of German secret weapons, and the Réseau AGIR reporting V-weapon installations in Occupied France to the British. Counterespionage included the use of turned Double Cross agents to misinform Nazi Germany of impact points during the Blitz and internment of Japanese in the US against "Japan's wartime spy program". Additional WWII espionage examples include Soviet spying on the US Manhattan project, the German Duquesne Spy Ring convicted in the US, and the Soviet Red Orchestra spying on Nazi Germany.
Spying has sometimes been considered a gentlemanly pursuit, with recruiting focused on military officers, or at least on persons of the class from whom officers are recruited. However, the demand for male soldiers, an increase in womens' rights, and the tactical advantages of female spies led the Special Operations Executive (SOE) to set aside any lingering Victorian Era prejudices and begin employing them in April 1942. Their task was to transmit information from Nazi occupied France back to Allied Forces. The main strategic reason was that men in France were at the risk of being interrogated by Nazi troops, and so women were safer and less likely to arouse suspicion. In this way they made good couriers and proved equal, if not more effective than their male counterparts. Their participation in Organization and Radio Operation was also vital to the success of many operations, including the main network between Paris and London.
- See also Honeypot
[edit] Espionage post World War II
In the United States, the Central Intelligence Agency operates a Clandestine Service (NCS).[14] Its mission is the clandestine collection of human intelligence (HUMINT) and covert action.[15]
[edit] Espionage technology and techniques
[edit] Spy fiction
An early example of espionage literature is Kim by the English novelist Rudyard Kipling, with a description of the training of an intelligence agent in the Great Game between the UK and Russia in 19th century Central Asia. An even earlier work was James Fenimore Cooper's classic novel, The Spy, written in 1821, about an American spy in New York during the Revolutionary War.
During the many 20th century spy scandals, much information became publicly known about national spy agencies and dozens of real-life secret agents. These sensational stories piqued public interest in a profession largely off-limits to human interest news reporting, a natural consequence of the secrecy inherent to their work. To fill in the blanks, the popular conception of the secret agent has been formed largely by 20th and 21st century literature and cinema. Attractive and sociable real-life agents such as Valerie Plame find little employment in serious fiction, however. The fictional secret agent is more often a loner, sometimes amoral'an existential hero operating outside the everyday constraints of society. Loner spy personalities may have been a stereotype of convenience for authors who already knew how to write loner private investigator characters that sold well from the 1920s to the present.
Johnny Fedora achieved popularity as a fictional agent of early Cold War espionage, but James Bond is the most commercially successful of the many spy characters created by intelligence insiders during that struggle. His less fantastic rivals include George Smiley.
[edit] See also
| Look up espionage in Wiktionary, the free dictionary. |
- Chinese Intelligence Operations in the United States
- Classified information
- Corporate espionage
- Covert United States foreign regime change actions
- Counter-espionage
- Dumpster diving
- Economic and Industrial Espionage
- Intelligence (information gathering)
- Labor spies
- List of cryptographers
- Military intelligence
- Mitrokhin Archive
- Mole (espionage)
- Ninja
- Operation Snow White
- Sabotage
- Safe house
- Security clearance
- Spymaster
- Stalker
- Wikileaks
[edit] Further reading
There is a vast and ever-growing body of literature devoted to espionage. The following reading list features some of the better known and more comprehensive accounts.
[edit] Surveys
| Author(s) | Title | Publisher | Date | Notes |
| Jenkins, Peter | Surveillance Tradecraft: The Professionals Guide to Surveillance Training | - | - | ISBN 978-9535378-22 |
| West, Nigel | MI6: British Secret Intelligence Service Operations 1909-1945 | - | 1983 | - |
| Smith Jr., W. Thomas | Encyclopedia of the Central Intelligence Agency | - | 2003 | popular |
| Richelson, Jeffery T. | The U.S. Intelligence Community | - | 1999 | fourth edition |
| Richelson, Jeffery T. | A Century of Spies: Intelligence in the Twentieth Century | - | 1977 | - |
| Owen, David | Hidden Secrets: A Complete History of Espionage and the Technology Used to Support It | - | - | - |
| O'Toole, George | Honorable Treachery: A History of U.S. Intelligence, Espionage, Covert Action from the American Revolution to the CIA | - | 1991 | - |
| Lerner, Brenda Wilmoth & K. Lee Lerner, eds. | Terrorism: essential primary sources | Thomas Gale | 2006 | ISBN 978-1-4144-0621-3 |
| Lerner, K. Lee and Brenda Wilmoth Lerner, eds. | Encyclopedia of Espionage, Intelligence and Security | - | 2003 | 1100 pages. 850 articles, strong on technology |
| Knightley, Philip | The Second Oldest Profession: Spies and Spying in the Twentieth Century | Norton | 1986 | - |
| Kahn, David | The Codebreakers: The Comprehensive History of Secret Communication from Ancient Times to the Internet | - | 1996 | Revised edition, 1200 pages. First published in 1967. |
| Johnson, Robert | Spying for Empire: The Great Game in Central and South Asia, 1757-1947 | London: Greenhill | 2006 | British Intelligence and its imperial connection |
| Friedman, George | America's Secret War: Inside the Hidden Worldwide Struggle Between the United States and Its Enemies | - | 2005 | since 9-11 |
| Bungert, Heike et al. eds. | Secret Intelligence in the Twentieth Century | - | 2003 | essays by scholars |
| May, Ernest (ed.) | Knowing One's Enemies: Intelligence Assessment before the Two World Wars | - | 1984 | - |
| Black, Ian and Morris, Benny | Israel's Secret Wars: A History of Israel's Intelligence Services | - | 1991 | - |
| Andrew, Christopher | For the President's Eyes Only: Secret Intelligence and the American Presidency from Washington to Bush | - | 1996 | - |
[edit] World War I
| Author(s) | Title | Publisher | Date | Notes |
| Tunney, Thomas Joseph and Paul Merrick Hollister | Throttled!: The Detection of the German and Anarchist Bomb Plotters | Boston: Small, Maynard & company | 1919 | Chapter 9 is about Capt Fritz Duquesne and is available on Wikisource: see text |
| Beesly, Patrick | Room 40 | - | 1982 | Covers the breaking of German codes by RN intelligence, including the Turkish bribe, Zimmermann telegram, and failure at Jutland. |
| Burnham, Frederick Russell | Taking Chances | - | 1944 | Chapter 2 is about Capt Fritz Duquesne Chapter 31 is about Howard Burnham |
| May, Ernest (ed.) | Knowing One's Enemies: Intelligence Assessment before the Two World Wars | - | 1984 | - |
| Tuchman, Barbara W. | The Zimmermann Telegram | Ballantine Books | 1966 | - |
[edit] World War II: 1931'1945
| Author(s) | Title | Publisher | Date | Notes |
| Babington-Smith, Constance | Air Spy: The Story of Photo Intelligence in World War II | - | 1957 | - |
| Bryden, John | Best-Kept Secret: Canadian Secret Intelligence in the Second World War | Lester | 1993 | - |
| Hinsley, F. H. and Alan Stripp | Codebreakers: The Inside Story of Bletchley Park | - | 2001 | - |
| Hinsley, F. H. | British Intelligence in the Second World War | - | 1996 | Abridged version of multivolume official history. |
| Hohne, Heinz | Canaris: Hitler's Master Spy | - | 1979 | - |
| Jones, R. V. | The Wizard War: British Scientific Intelligence 1939-1945 | - | 1978 | - |
| Kahn, David | Hitler's Spies: German Military Intelligence in World War II' | - | 1978 | - |
| Kahn, David | Seizing the Enigma: The Race to Break the German U-Boat Codes, 1939-1943 | - | 1991 | FACE |
| Kitson, Simon | The Hunt for Nazi Spies: Fighting Espionage in Vichy France | - | 2008 | |
| Lewin, Ronald | The American Magic: Codes, Ciphers and the Defeat of Japan | - | 1982 | - |
| Masterman, J. C. | The Double Cross System in the War of 1935 to 1945 | Yale | 1972 | - |
| Persico, Joseph | Roosevelt's Secret War: FDR and World War II Espionage | - | 2001 | - |
| Persico, Joseph | Casey: The Lives and Secrets of William J. Casey-From the OSS to the CIA | - | 1991 | - |
| Ronnie, Art | Counterfeit Hero: Fritz Duquesne, Adventurer and Spy | - | 1995 | ISBN 1-55750-733-3 |
| Sayers, Michael & Albert E. Kahn | Sabotage! The Secret War Against America | - | 1942 | - |
| Smith, Richard Harris | OSS: The Secret History of America's First Central Intelligence Agency | - | 2005 | - |
| Stanley, Roy M. | World War II Photo Intelligence | - | 1981 | - |
| Wark, Wesley | The Ultimate Enemy: British Intelligence and Nazi Germany, 1933-1939 | - | 1985 | - |
| Wark, Wesley | "Cryptographic Innocence: The Origins of Signals Intelligence in Canada in the Second World War" in Journal of Contemporary History 22 | - | 1987 | - |
| West, Nigel | Secret War: The Story of SOE, Britain's Wartime Sabotage Organization | - | 1992 | - |
| Winterbotham, F. W. | The Ultra Secret | Harper & Row | 1974 | - |
| Winterbotham, F. W. | The Nazi Connection | Harper & Row | 1978 | - |
| Cowburn, B. | No Cloak No Dagger | Brown, Watson, Ltd. | 1960 | - |
| Wohlstetter, Roberta. | Pearl Harbor: Warning and Decision | - | 1962 | - |
[edit] Cold War era: 1945'1991
| Author(s) | Title | Publisher | Date | Notes | |
| Aldrich, Richard J. | The Hidden Hand: Britain, America and Cold War Secret Intelligence | - | 2002 | - | |
| Ambrose, Stephen E. | Ike's Spies: Eisenhower and the Intelligence Establishment | - | 1981- | - | |
| Andrew, Christopher and Vasili Mitrokhin | The Sword and the Shield: The Mitrokhin Archive and the Secret History of the KGB | Basic Books | 1991, 2005 | ISBN 0465003117 | |
| Andrew, Christopher, and Oleg Gordievsky | KGB: The Inside Story of Its Foreign Operations from Lenin to Gorbachev | - | 1990 | - | |
| Aronoff, Myron J. | The Spy Novels of John Le Carré: Balancing Ethics and Politics | - | 1999 | - | |
| Bissell, Richard | Reflections of a Cold Warrior: From Yalta to the Bay of Pigs' | - | 1996 | - | |
| Bogle, Lori, ed. | Cold War Espionage and Spying | - | 2001- | essays | |
| Christopher Andrew and Vasili Mitrokhin | The World Was Going Our Way: The KGB and the Battle for the Third World | - | - | - | |
| Christopher Andrew and Vasili Mitrokhin | The Mitrokhin Archive: The KGB in Europe and the West | Gardners Books | 2000 | ISBN 978-0-14-028487-4 | |
| Colella, Jim | My Life as an Italian Mafioso Spy | - | 2000 | - | |
| Craig, R. Bruce | Treasonable Doubt: The Harry Dexter Spy Case | University Press of Kansas | 2004 | ISBN 978-0-7006-1311-3 | |
| Dorril, Stephen | MI6: Inside the Covert World of Her Majesty's Secret Intelligence Service | - | 2000 | - | |
| Dziak, John J. | Chekisty: A History of the KGB | - | 1988 | - | |
| Gates, Robert M. | From The Shadows: The Ultimate Insider's Story Of Five Presidents And How They Won The Cold War' | - | 1997 | - | |
| Frost, Mike and Michel Gratton | Spyworld: Inside the Canadian and American Intelligence Establishments | Doubleday Canada | 1994 | - | |
| Haynes, John Earl, and Harvey Klehr | Venona: Decoding Soviet Espionage in America | - | 1999 | - | |
| Helms, Richard | A Look over My Shoulder: A Life in the Central Intelligence Agency | - | 2003 | - | |
| Koehler, John O. | Stasi: The Untold Story of the East German Secret Police' | - | 1999 | - | |
| Persico, Joseph | Casey: The Lives and Secrets of William J. Casey-From the OSS to the CIA | - | 1991 | - | |
| Murphy, David E., Sergei A. Kondrashev, and George Bailey | Battleground Berlin: CIA vs. KGB in the Cold War | - | 1997 | - | |
| Prados, John | Presidents' Secret Wars: CIA and Pentagon Covert Operations Since World War II | - | 1996 | - | |
| Rositzke, Harry. | The CIA's Secret Operations: Espionage, Counterespionage, and Covert Action | - | 1988 | - | |
| Srodes, James | Allen Dulles: Master of Spies | Regnery | 2000 | CIA head to 1961 | |
| Sontag Sherry, and Christopher Drew | Blind Man's Bluff: The Untold Story of American Submarine Espinonage | Harper | 1998 | ||
| Encyclopedia of Cold War Espionage, Spies and Secret Operations | Greenwood Press/Questia | 2004 | - |
[edit] Post Cold War era: 1992'present day
| Author(s) | Title | Publisher | Date | Notes |
| Anderson, Nicholas | NOC | Enigma Books | Nicholasanderson.info 2008 eBook and Enigma Books., 2009 | |
| Ishmael Jones | The Human Factor: Inside the CIA's Dysfunctional Intelligence Culture | Encounter Books | 2008, rev. 2010 | deep cover espionage |
| Michael Ross | The Volunteer: The Incredible True Story of an Israeli Spy on the Trail of International Terrorists | McClelland & Stewart | 2007, rev. 2008 | deep cover espionage |
[edit] References
| This article includes a list of references, but its sources remain unclear because it has insufficient inline citations. Please help to improve this article by introducing more precise citations where appropriate. (April 2009) |
- ^ "Espionage in Ancient Rome". HistoryNet.
- ^ Henrywotton.org.uk
- ^ Suvorov, Victor (1987). Inside the Aquarium. Berkley. ISBN 042509474X.
- ^ US Department of Defense (2007-07-12). "Joint Publication 1-02 Department of Defense Dictionary of Military and Associated Terms" (PDF). http://www.dtic.mil/doctrine/jel/new_pubs/jp1_02.pdf. Retrieved 2007-10-01.
- ^ "Defectors say China running 1,000 spies in Canada". CBC News. June 15, 2005.
- ^ "Beijing's spies cost German firms billions, says espionage expert". The Sydney Morning Herald. July 25, 2009.
- ^ Agent Websters Online Dictionary
- ^ Agent UK Mi5.gov -How spies operate.
- ^ Double Agent Cia.gov
- ^ Agent types provided by: Harry Ferguson -Spy: A Handbook.
- ^ Cia.gov
- ^ Illegal Mi5.gov -How spies operate.
- ^ Famous Spies in History, CNN
- ^ www.cia.gov. CIA > Offices of CIA > Clandestine Service > Who We Are. Retrieved 2010-06-18.
- ^ www.cia.gov CIA > Offices of CIA > Clandestine Service > Our Mission. Retrieved 2010-06-18.
[edit] External links
| Wikiquote has a collection of quotations related to: Espionage |
- An Interactive Rosenberg Espionage Ring Timeline and Archive
- GCHQ: Britain's Most Secret Intelligence Agency
|
||||||||||||||||||||||
|
SOURCES.COM is an online portal and directory for journalists, news media, researchers and anyone seeking experts, spokespersons, and reliable information resources. Use SOURCES.COM to find experts, media contacts, news releases, background information, scientists, officials, speakers, newsmakers, spokespeople, talk show guests, story ideas, research studies, databases, universities, associations and NGOs, businesses, government spokespeople. Indexing and search applications by Ulli Diemer and Chris DeFreitas.
For information about being included in SOURCES as a expert or spokesperson see the FAQ or use the online membership form. Check here for information about becoming an affiliate. For partnerships, content and applications, and domain name opportunities contact us.